Unlocker API
 Simulate real browser fingerprints
Simulate real browser fingerprints
 Intelligent anti-detection, automatically avoid bans
Intelligent anti-detection, automatically avoid bans
 Pay based on successful results
Pay based on successful results
 Automatic captcha recognition and proxy rotation.
Automatic captcha recognition and proxy rotation.

Professional network unlocking and web crawling solutions

Intelligent Multi-Strategy Unlock
Integrated AI dual-rule engine, automatically recognising the type of website restrictions (geographical restrictions / anti-scraping verification / content review) and dynamically matching unlocking strategies (such as proxy pool switching, automatic captcha bypass, request header spoofing).
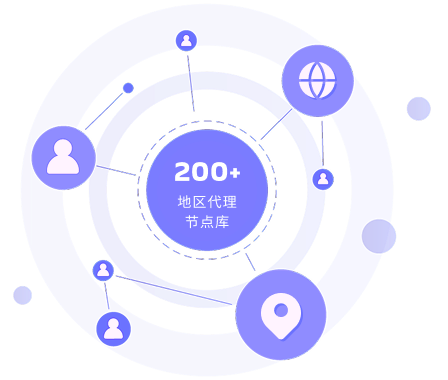
Regional precise agent scheduling
Based on a global database of proxy nodes across 200 regions, it supports intelligent scheduling of the optimal proxy according to the target website’s service node location (rather than just the user-specified region), while simultaneously monitoring the proxy’s latency and packet loss in real time, achieving millisecond-level failover.

JS rendering integrated with anti-anti-crawling
Built-in headless browser engine, automatically handles website JS rendering and dynamic content loading, while integrating anti-scraping protection (such as fingerprint obfuscation and dynamic control of request frequency), outputting either ‘fully rendered HTML’ or ‘structured data’ results.
Use IPFLY to bypass the captcha
We provide a visual integration console, environment pre-validation tools, and enhanced debugging templates. You can easily integrate our solutions into your projects, and we guarantee that you can quickly and easily launch web crawler projects.
Network Unlocker API Pricing

Deeply aligned with the high-level business needs of top-tier enterprises.
 Consult now
Consult now
-
 Dedicated account manager
Dedicated account manager
-
 Infinite scalability
Infinite scalability
-
 Custom package
Custom package
-
 Precision service
Precision service
-
 Full protocol support
Full protocol support
-
 Data monitoring dashboard
Data monitoring dashboard
We accept these payment methods:
IPFLY Network Unlocking Solution

Amazon/Taobao product page unlocked

Facebook/Twitter content scraping

Google/Bing ranking monitoring

Dynamic page rendering on Ctrip/Expedia

Bloomberg/Reuters data acquisition

News website unblock
Trusted by 100,000+ Customers Worldwide


















































Outstanding customer experience in the industry
Browser API FAQ
What are the core features of the Network Unlocker API?
It is mainly used to break through web page access restrictions (such as anti-crawling detection and access interception). It can also automatically complete verification code identification and agent resource scheduling to help stably obtain targeted web page data without manual intervention in the entire process.
How does it make requests closer to real user operations?
By simulating real browser fingerprints (restoring the browser environment characteristics of normal users) and using an intelligent anti-detection engine to dynamically adapt website rules, the requested behavior and parameters are more in line with the browsing habits of real users.
What types of verification codes can it handle automatically?
Supports automatic recognition of a variety of common verification codes, including graphic character verification codes, slider verification, click-type verification, etc., and can complete the process without manual verification.
Do I need to prepare proxy IP resources myself when using it?
No, the API has a built-in proxy automatic switching function, which will dynamically schedule available proxy resources according to access scenarios, eliminating the need to manually configure or maintain a proxy pool.
What will the API do if a website is temporarily blocked?
The intelligent avoidance mechanism will be triggered -automatically retry the request, adjust access parameters (such as browser fingerprints), switch resources such as proxies, and try to re-establish a valid connection to complete data acquisition.
Is it easy for users with non-technical backgrounds to get started?
Easy, the API adopts a "plug and play" packaging form, and the interface design is simple. You only need to set basic parameters such as the target URL and data requirements according to the guidelines to initiate a request, without complex technical configuration.






















